1. What's OP-TEE[edit | edit source]
OP-TEE is an open-source software component hosted by Trusted Firmware[1] organization. It allows the development and integration of services and applications running on Cortex-A trusted execution environment (also called secure context), that is isolated from Cortex-A nonsecure context running the Linux® -based OS.
Description extracted from the OP-TEE site[2]:
- "OP-TEE is a Trusted Execution Environment (TEE) designed as companion to a nonsecure Linux kernel running on Arm; Cortex-A cores using the TrustZone technology. OP-TEE implements TEE Internal Core API v1.1.x which is the API exposed to Trusted Applications and the TEE Client API v1.0, which is the API describing how to communicate with a TEE. Those APIs are defined in the GlobalPlatform API specifications."
OP-TEE is delivered under a BSD style license and can run secure (trusted) applications, named TAs, without restriction on their licensing model. It allows customers to reuse STM32 MPU support developed by ST in the TEE of their choice.
For more details about OP-TEE open-source project and internal architecture, please refer to OP-TEE concepts overview.!
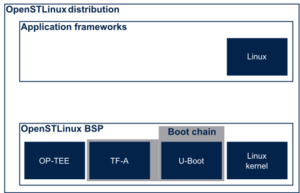
2. OP-TEE roles in OSTL[edit | edit source]
ST made the choice to implement OP-TEE in all STM32 Arm® Cortex® MPUs ![]() for several reasons:
for several reasons:
- To have an open-source solution for Arm® Cortex®-A secure context which can be a reference implementation for customers.
- To have the same boot architecture for secure and nonsecure devices to ease customer life if he wants to activate security during his project development.
- To support firmware update including platform system configuration without impacting FSBL. Indeed OP-TEE binary is part of FIP image which can easily be updated at the same time of the Linux distribution. FSBL could be considered as immutable.
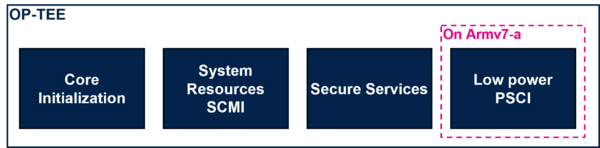
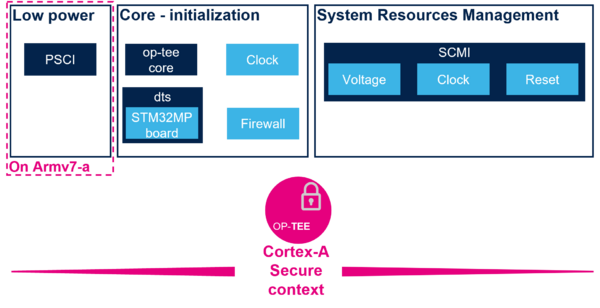
In OSTL implementation, OP-TEE is responsible for:
- System configuration at boot time: that means preparing the platform for applications and processor execution by configuring all system resources like clock tree, memory and peripheral firewalls, bus QoS etc...
- System resource management at runtime: that means providing services based on SCMI API [1] to access resources that are either exclusively controlled by Cortex-A secure context or that are shared between several execution contexts. In this last case, system resource management services act as platform arbiter.
- Secure services at runtime: based on GlobalPlatform TEE API specifications, they provide secure services like cryptographic operations, secure storage, random number generator, trusted coprocessor management or user trusted application support. All services can be enabled or disabled according to customer product requirements.
On STM32MP1 series, due to Armv7-A architecture limitation, OP-TEE is also implementing:
- Low-power Arm® Cortex®-A management: based on PSCI standard API [2], OP-TEE is providing Cortex-A and system low-power support.
3. OP-TEE profiles[edit | edit source]
To easily adapt OP-TEE content to customer product needs, ST proposes different profiles:
- System services profile
- Secure service profile
OP-TEE profile can be selected by compilation flag CFG_STM32MP_PROFILE, detailed in OP-TEE profiles article.
3.1. System services profile[edit | edit source]
CFG_STM32MP_PROFILE=system_services
In the mode, OP-TEE is limited to system resources initialization and management.
It configures clock tree and firewall according to Device Tree configuration and provide SCMI server.
OP-TEE also provides BSEC OTPs access, low power management and other system services. Refer to system services for more information.
The following figure shows an overview of OP-TEE services in this configuration.
3.2. Secure Service profile[edit | edit source]
CFG_STM32MP_PROFILE=secure_and_system_services
In addition to system services, this profile enables OP-TEE secure services including trusted applications (TAs) support. More information in the secure and system services article.
The following figure shows an overview of OP-TEE services in this configuration.

| Note that even if it is possible to disable system resource management support in OP-TEE, ST doesn't recommend this option in order to guarantee integrity of peripherals used by Cortex-A secure context. |
4. OP-TEE overview per STM32 MPU device[edit | edit source]
OP-TEE content depends also on the microprocessor device and the related peripherals that should be managed by Arm® Cortex®-A secure context.
Please refer to sub-article corresponding to the STM32 MPU you use for more details.
| STM32 MPU devices | Associated articles |
|---|---|
| STM32MP13x lines |
STM32MP13 OP-TEE overview |
| STM32MP15x lines |
STM32MP15 OP-TEE overview |
| STM32MP2 series | STM32MP2 OP-TEE overview |